Securing your website
I take a look at a few things you can do to secure your HTTPS website even further
In the first three parts of this series, I discussed the value proposition of HTTPS, what SSL certificates are and how to get one for free, and additional things you can do to secure your website even further.
It’s time to wrap up the series by taking a look at some HTTPS blind spots and why securing your website does not stop at serving content securely.
HTTPS does protect against many common attacks often spawned by a Man In The Middle, but it cannot stop hackers from breaking into your web server or network. The “Secure” part in HTTPS only refers to the security of your connection to a website. It’s got nothing to do with the security of the infrastructure that a website has on its back end.
By serving your website over HTTPS, you are ensuring that data sent from or to your server will not be compromised when in transit between the client and the server. But if your server is hacked, you’ve got much bigger problems on your hands. An attacker can easily manipulate your site’s content or steal the information of your users. And HTTPS cannot protect against that.
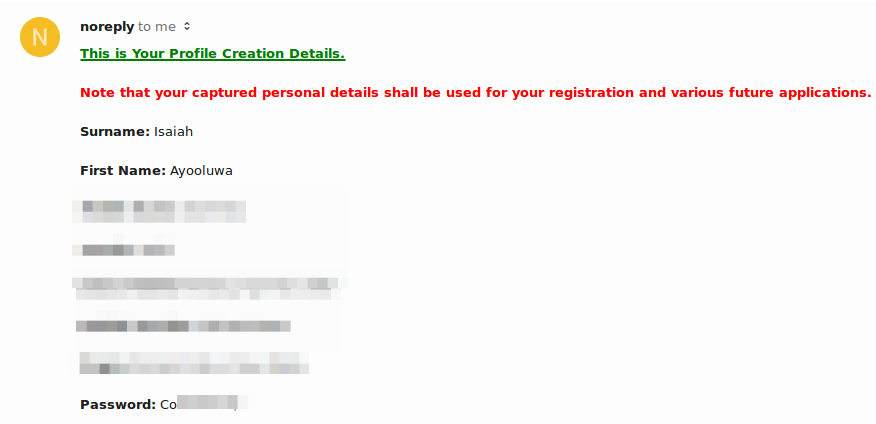
So securing a website is much more than just serving its content over HTTPS. You still need to practice good security habits on the server side. Encrypting data when in transit is not enough, you also need to make sure that nothing is stored in plain text on the server side. This is especially important for sensitive user data such as passwords or card information.
A lot data breaches occur despite the presence of HTTPS, so if you neglect security on the back end, you will be at risk of being compromised just like Equifax, Ashley Madison, LinkedIn and others. And this can be very damaging to a business.
Here’s the thing, HTTPS does not guarantee that a website is safe to use. Phishers, Scammers and Malware producers can also serve their websites using HTTPS in a bid to boost their legitimacy in your eyes. Even legit websites can be compromised on the server side and made to distribute malware securely.
It’s a lot like receiving a package from overseas. HTTPS only ensures that the package reaches your address safely with its seal intact. It knows nothing about the contents of the package or the entity that sent it.
You wouldn’t blindly trust a random person in uniform, so don’t assume that a site is safe just because the browser shows a green padlock in the address bar.
I talked about this a little bit in part 3 where I gave an example of a banking website that didn’t think it was important to serve their homepage over HTTPS and why you should not indulge in this practice.
Just to reiterate, implementing HTTPS on some pages and not on others creates an unnecessary risk, and dilutes the benefits of having that secure layer in the first place. This point is often lost on many businesses.
So do serve all content with HTTPS. There is no downside to doing this.
HTTPS is only a part of the puzzle, albeit a crucial one. It’s not going to stop websites from being hacked, the distribution of malware or data breaches.
However, it greatly reduces the risk of data in transit being exploited by attackers and it’s the only outwardly facing assurance we have that a website takes the security and privacy of its users seriously.
Comments
Ground rules
Please keep your comments relevant to the topic, and respectful. I reserve the right to delete any comments that violate this rule. Feel free to request clarification, ask questions or submit feedback.